UK: 03330 156 651 | IE: 01263 5299
-
UK: 03330 156 651
-
IE: 01263 5299
The Axios Supply Chain Attack: What It Means for Your Business
You might have seen the recent news about the Axios supply chain attack. For many business owners, the immediate question is simple: “Does this actually...
- Published Date:
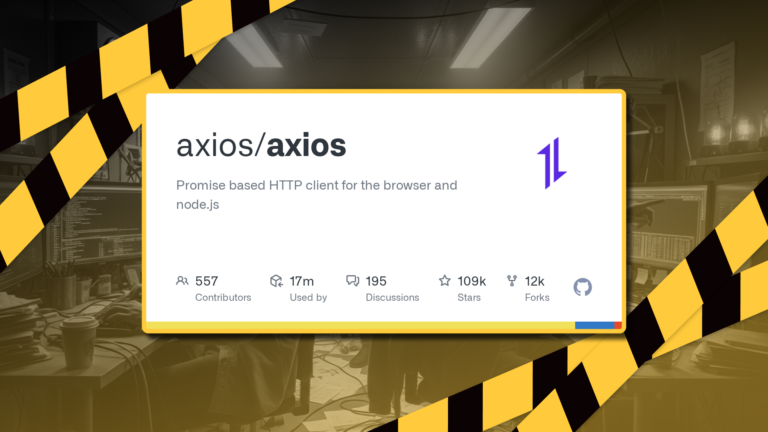
Table of Contents
You might have seen the recent news about the Axios supply chain attack. For many business owners, the immediate question is simple: “Does this actually affect us?”
The short answer is: potentially, but not in the way you might expect.
This isn’t about hackers trying to break into your business directly. It’s about something quieter. A trusted piece of software, working behind the scenes, becomes the entry point for an attack.
In this guide, we’ll explain what Axios does, how these supply chain attacks happen, and the practical steps you can take today to keep your business secure.
Check out the Video below from Cybersecurity Guru and Ethical Hacker John Hammond if you want more information about who’s affected and how the hack was executed:
What Axios Actually Is
Axios is a highly popular piece of open-source software known as a JavaScript library. When software developers build applications, they need a way for different systems to send and receive data over the internet. Writing this communication code from scratch is complicated and repetitive. Axios simplifies this by handling HTTP requests—the digital “handshakes” that let a web browser or a server talk to another server.
Who Uses It
You won’t find Axios as a standalone app installed on your desktop. Instead, it is used by software developers worldwide as a foundational building block. Because it simplifies complex code so well, developers build it directly into the software that businesses rely on daily. You will find it inside:
- The websites and portals your team logs into: When you open a cloud accounting dashboard, your customer CRM, or an online booking system, Axios is often the tool working in the background to fetch your records and display them on your screen.
- The invisible systems that process your data: When a customer clicks “submit” on a payment page, Axios is often the secure digital messenger that carries the transaction details from the website directly to the payment processor.
- The automated systems that update your software: When a software provider rolls out a new feature or a bug fix overnight without taking the whole system offline, they often rely on automated, behind-the-scenes tools powered by Axios to deliver those updates smoothly.
Why It’s So Popular (The Figures)
Axios is the most popular JavaScript library of its kind because it gives developers a simple, reliable way to make internet requests across different environments.
To understand its reach, look at the numbers:
- It averages over 100 million downloads every single week.
- It is so widely adopted that it is present in virtually every modern JavaScript codebase that needs to make HTTP requests.
The Business Impact
This immense popularity is exactly why it was targeted. When a tool has over 100 million weekly downloads, attackers know that compromising it creates a massive “blast radius”. By slipping malicious code into a trusted Axios update, hackers don’t have to break into thousands of individual businesses manually. The automated systems and developers building your software simply download the compromised update for them during routine installations.
This reinforces why modern cybersecurity isn’t just about protecting your own laptops—it’s about monitoring the trusted, behind-the-scenes tools your business software relies on.

What Is a Supply Chain Cyber Attack?
A supply chain attack is like a thief compromising a lock at the factory before it’s even installed on your door.
The attackers don’t target your business directly. Instead, they tamper with a trusted building block—like Axios. Because your software trusts that building block, the attackers gain a silent, trusted pathway into your systems when the software updates.
How These Attacks Actually Unfold
One of the biggest misconceptions about cyber attacks is that they are immediate and obvious. In reality, they happen in quiet stages:
- Silent Entry: A compromised update runs in the background. No alarms go off, and everything appears to be working normally.
- Data Exposure: Attackers quietly capture login details and system access tokens. This is the stage where your business is most exposed.
- Expansion: Using those stolen credentials, the attackers move into your email accounts, finance tools, and CRM.
- Disruption: Eventually, the attackers make their presence known—often by deploying ransomware or locking you out of your data. By this point, they may have been inside your network for weeks.
The Key Risk: It’s Not Just Devices — It’s Access
Small and medium-sized businesses rely heavily on third-party software, which naturally expands the areas where an attack can happen.
It’s easy to think, “If a laptop is infected, we’ll just turn it off.” While isolating a device helps, it doesn’t solve the core problem. The attackers are ultimately after your login credentials and cloud access. Once they have your passwords, they don’t need your infected laptop anymore; they can log into your systems from anywhere in the world.

Practical Steps to Protect Your Business
To defend against supply chain attacks, you need a dependable, multi-layered approach. Here are the practical steps you should take:
- Keep everything patched and updated: Outdated software is an open door for attackers. Tools like Advanced Patching automatically update non-Microsoft apps like Chrome or Zoom to keep them secure and up-to-date. This removes the hassle of manual updates and ensures your business is protected against known vulnerabilities.
- Don’t rely on passwords alone: Changing passwords after a breach is important, but it’s not enough. Adding Multi-Factor Authentication (MFA) and ensuring users are logged out of compromised sessions means that even if a password is stolen, your systems remain secure.
- Monitor for credential exposure: Many attacks are only discovered after stolen passwords appear online. Dark Web Monitoring identifies compromised credentials early to prevent unauthorised access to sensitive data. Finding these leaks early lets you secure your accounts before they can be used against you.
- Scan for network vulnerabilities: You can’t fix what you can’t see. Automated Vulnerability Scanning routinely checks your network to find exposed devices before hackers do. It turns complex security data into a simple, prioritized list of weaknesses, showing exactly what to fix first without confusing technical logs.
- Detect behaviour, not just known threats: Traditional security looks for familiar viruses, but modern attacks are more subtle. Installing an Endpoint Detection and Response (EDR) software acts as a digital detective that looks for strange behaviour on your computer, investigates it, and stops attacks before they spread.
- Keep ransomware protection active: Even if ransomware isn’t the initial entry point, it’s often the final payload. In the event software misses a threat, a managed Security Operations Centre (SOC) team spots the unusual behaviour and isolates the machine before the attack spreads.
- Isolate devices, but act fast: If an infection is detected, isolating the compromised device immediately stops the malware from moving across your network. However, this must be combined with locking down access and resetting credentials to be fully effective.
- Train your team: Cyber attacks frequently rely on human error to succeed. Empower your team to spot scams with Security Awareness Team Training that firewalls miss with engaging and customisable training modules. When your staff know what to look for, they become an active layer of your business defence.
The Bottom Line: Trust is the New Attack Surface
The Axios attack highlights a practical reality for modern businesses: security isn’t just about what you install, but what your software relies on. Your daily operations depend on cloud platforms, integrations, and third-party code.
This doesn’t mean your systems are currently compromised. It just means that passwords alone won’t protect you, and having tools to detect unusual activity is just as important as trying to prevent it in the first place.
Need help? Our team is here to keep things running smoothly. If you’re unsure how exposed your business is, start with a simple review. We’ll help you find a straightforward cybersecurity setup that fits your business and your budget.
Speak to a specialist about your cybersecurity posture today: https://yellowcom.co.uk/enquiry-form/

Useful Resources
Microsoft: Mitigating the Axios npm supply chain compromise
Google Cloud Threat Intelligence: North Korea-Nexus Threat Actor Compromises Widely Used Axios NPM Package in Supply Chain Attack
Unit 42 Threat Brief: Widespread Impact of the Axios Supply Chain Attack

Looking for a Smarter Way to Stay Connected? We Help Businesses Cut Costs and Improve Communication.
Share this post:
SHARE POST
Related Posts
What is a business cloud phone system? A business cloud phone system (also called hosted VoIP) is a phone.
Your business is growing, and that is a fantastic thing. You are taking on new customers, hiring new staff,.
For many organisations across Ireland, telecoms is a necessary but often overlooked expense. From Dublin offices to regional businesses.